Agent‑Safe Tools
How it works
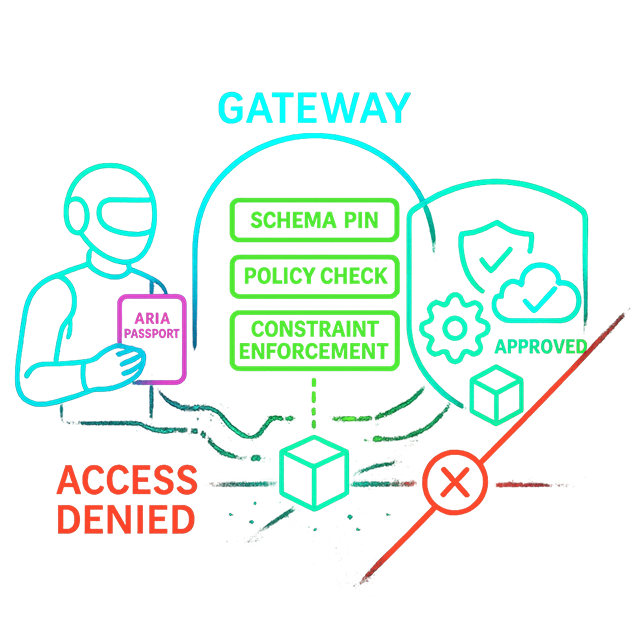
- Agent presents ARIA Passport to Gateway.
- Gateway validates and checks policy for the requested tool.
- Constraints and obligations enforced; tool is invoked.
- Receipt is created with full context.
What the PDP returns for an agent tool call
When an agent calls tools/invoke, the PDP checks delegation, verifies the tool is in the agent's capability list, and returns a permit with agent-specific constraints and obligations stacked on the decision:
Constraints returned
- Model allowlist (e.g., gpt-4o-mini only)
- Token / output cap
- Egress allowlist (approved API hosts)
- Spend budget (daily/monthly per-model)
- Data scope (delegating user's ABAC scope)
Obligations returned
audit_log— full decision contextrate_limit— per-agent velocity- Signed receipt emission
- Notification on high-risk permits
Same PDP, same AuthZEN wire format. Agent path requires delegation_id + tool in delegation_capabilities. Human path requires only PermissionGrant. Both get constraints. Authorization engine →
FAQ
- How do schema pins work? Gateway validates tool/model schema hash/version and blocks drift pre‑exec.
- Can we restrict tools per agent? Yes. AuthZEN constraints and allow‑lists per agent/role.
- Do we get receipts? Every governed call emits a signed receipt for audit and chargeback.
Related comparisons
Watch: Tool Governance in 90 seconds
Standards
- OpenID AuthZEN obligations/constraints
- RAR (RFC 9396), DPoP (RFC 9449)
- MCP model/tool schema pins