Put AI agents into production safely.
Runtime execution control for AI agents
ARIA gives security teams runtime execution control over agents: authorize every action, isolate credentials, require approval for risky steps, and produce cryptographic proof of what executed.
Agents are shipping. Controls are not.
Every organization deploying AI agents faces the same four gaps between capability and control.
Shared identities and broad tokens make accountability blurry. Who authorized this action? Nobody can answer.
Delete, charge, revoke, or escalate — it happens instantly. No human approval step in the path.
Security teams cannot prove what was approved, why it was allowed, and what actually executed. Logs can be forged or deleted.
Most teams learn about overspend and overreach too late. Budget caps and scope limits are afterthoughts.
Others discover and inventory.
We govern what agents actually do.
Three architectural properties make this possible.
OAuth Vault
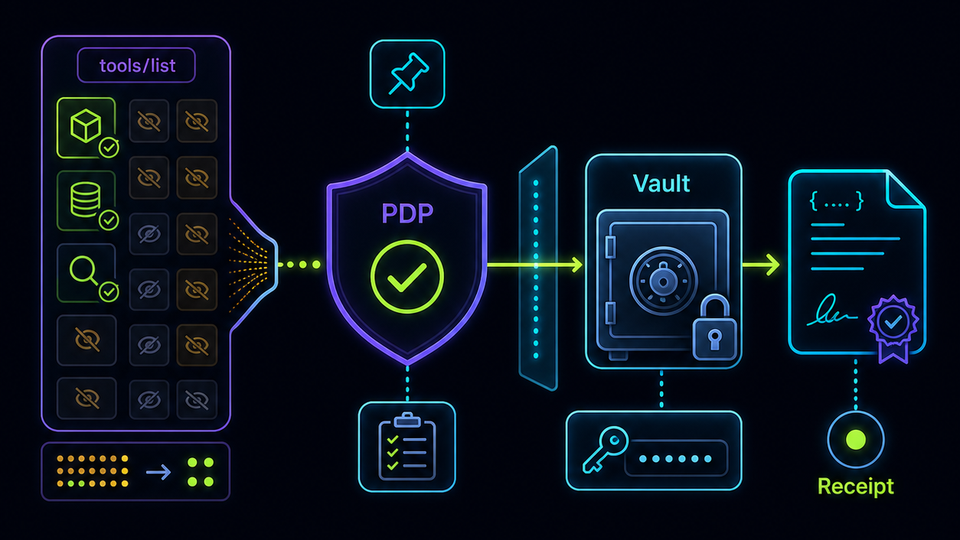
Tokens never leave the server. Not a configuration option — an architectural property. The PDP authorizes, the vault retrieves, the target system receives. The agent never sees credentials. XSS-proof, logging-proof, developer-misuse-proof.
Every competitor passes credentials through the agent layer.
How the zero-trust vault works →Approval-Before-Act
Every agent action gets Allow, Deny, or Escalate. Risky actions route to human review with bounded reasoning and evidence digests. Single-use execution token guarantees exactly-once execution. No replays.
Not a simple approval flow. Governance with teeth.
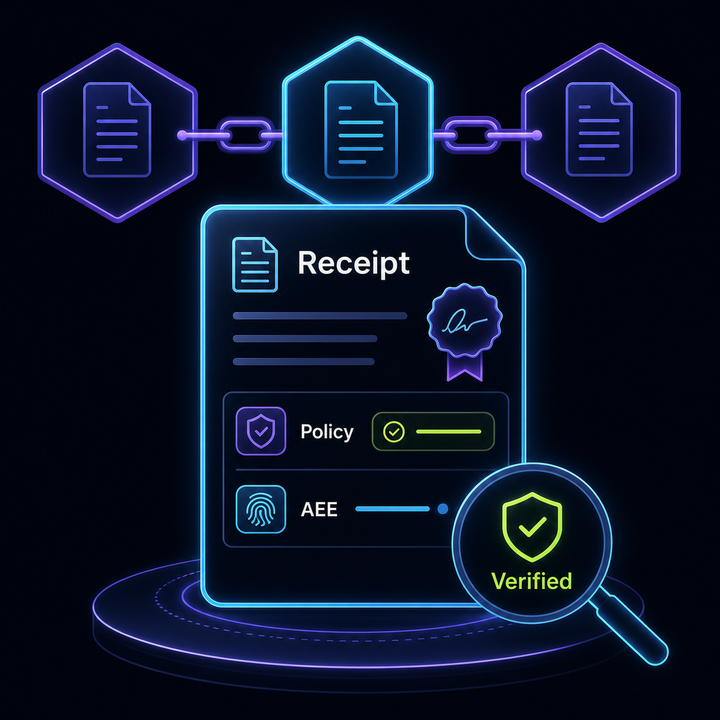
Cryptographic Proof Chain
Per-action evidence packs — not logs. Request, policy decision, execution result, AEE fingerprint. Each receipt hash-chained to the previous. Tamper-evident and regulatory-ready.
Prove what happened, to anyone, anytime.
Deploy Your Way
Two buying motions. One trust stack.
ARIA Control
Govern the agents you already have
Keep your current agent stack — Dify, Langflow, n8n, custom MCP clients, or any orchestration platform. ARIA adds runtime authorization, approval gates, credential isolation, and proof without rebuilding your stack. No agent code changes.
Best for: existing agent stacks, security and platform teams
ARIA Enterprise
Everything in Control, plus your own agents
Build and run governed agents on EmpowerNow's platform — visual workflow designer, agent lifecycle management, FinOps controls, and Sentinel for governed browser, desktop, and mobile execution. Full control plane with the same trust stack built in.
Explore EmpowerNow AI Agents →Best for: custom governed agents, high-risk execution, regulated automation
How ARIA Works
Is this agent allowed to perform this action?
The token is used, not exposed. Server-side only.
Allow, deny, or require human approval.
The worker gets a governed instruction, not raw authority.
Request, decision, execution, outcome — hash-chained.
Five steps. One screen. Every action authorized, isolated, and proven.
Technical deep-dive Deep dive: SSC governance, OAuth Vault three-zone model, and the WAITING protocol
Policy Gateway (Five-Rails Pipeline)
Every agent request passes through five sequential checks: (1) Schema pin — the tool's input/output schema is verified against a SHA-256 hash. (2) Delegation verification — the agent's delegation chain is validated. (3) PDP evaluation — the AuthZEN PDP evaluates the request against active policy. (4) Constraint application — budget caps, TTL limits, and rate limits. (5) Identity chaining — OBO token exchange binds the action to the delegating user. All five must pass. Fail-closed.
OAuth Vault (Three-Zone Credential Isolation)
Credentials never touch the agent's memory, logs, or inference chain. Zone 1 (Authorization) — the PDP decides whether the agent is authorized. Zone 2 (Retrieval) — the vault retrieves the credential and injects it into the outbound request. Zone 3 (Execution) — the target system receives the request. The agent never sees Zones 2 or 3.
The PDP: Single Policy Brain for Every Agent Action
Every ARIA enforcement decision — tool authorization, delegation verification, budget enforcement, egress control — is an AuthZEN evaluation against the same PDP that governs human UI access, IGA governance rules, and identity token issuance. One policy language. One audit trail. Constraints (spend caps, egress allowlists, PII redaction) and obligations (audit log, receipt emission) ride in the standard AuthZEN context — not a parallel protocol.
Structured Safety Case (SSC) / WAITING Protocol
For high-risk actions, the PDP returns Escalate. The agent produces a structured justification with bounded reasoning, SHA-256 evidence digests, risk band, and confidence score. A human reviewer approves or rejects. On approval, a single-use execution token with atomic JTI consumption is minted — exactly-once execution. No replays. No duplicate executions.
Signed Execution + Proof Chain
The approved action is wrapped in a signed envelope and dispatched. On completion, an evidence pack is assembled: request, PDP decision (with policy hash), execution result, and AEE fingerprint. This receipt is hash-chained to the previous receipt — tamper-evident audit trail. Auditors get cryptographic proof, not log files.
credentials exposed
to the agent layer
of agent actions
auditor-verifiable
exactly-once execution
on every risky action
EU AI Act ready
Articles 14 & 53 mapped
See It in Action
How ARIA Compares
Capability-by-capability, against the platforms you are already evaluating.
| Capability | ARIA | Okta | CyberArk | SailPoint | ServiceNow | Microsoft |
|---|---|---|---|---|---|---|
| Pre-execution runtime authorization | ✓ | Partial | — | — | Partial | Partial |
| Credential isolation (tokens never leave server) | ✓ | — | PAM* | — | — | — |
| Approval-before-act with exactly-once execution | ✓ | — | — | — | Workflow | — |
| Cryptographic proof chain (not logs) | ✓ | — | — | — | — | — |
| Policy-scoped tool discovery | ✓ | — | — | — | — | — |
| BYO agent platform support | ✓ | — | — | — | Partial | Copilot only |
| Standards-based (OAuth 2.0 + AuthZEN + MCP) | ✓ | Partial | Proprietary | Proprietary | Proprietary | Partial |
* CyberArk PAM vaults credentials but retrieves them into the agent session — credentials are exposed to the agent runtime.
Partial = supports some aspect of this capability but not purpose-built for agent runtime execution control. Based on publicly available product documentation as of March 2026.
Who Uses ARIA
Govern Your Existing Agent Stack
Running agents on Dify, Langflow, n8n, or a custom orchestration with no way to enforce approvals or prove actions. Add ARIA Control as a runtime layer — no rip and replace.
Approval-Before-Act for High-Risk Actions
Agents that delete records, charge accounts, or modify user data. Route through SSC with defined approvers, evidence requirements, and escalation chains. Agents wait.
Regulated Industries
Financial services, healthcare, or any sector where regulators require proof of what AI systems did. ARIA's proof chain and EU AI Act mapping deliver auditor-ready evidence, not log files.
Don't just govern agents. Run them.
ARIA Enterprise includes EmpowerNow's own governed agents — 170+ interactive workflows, Sentinel autonomous monitors, and a visual agent builder — all running on the same trust stack described above. Every action authorized, every credential isolated, every outcome proven.
Ready to put agents into production safely?
We'll show you how ARIA authorizes actions at runtime, isolates credentials, routes high-risk steps to approval, and produces proof your auditors can verify.