Set one policy. Enforce everywhere. Prove everything.
The governed action layer for the enterprise.
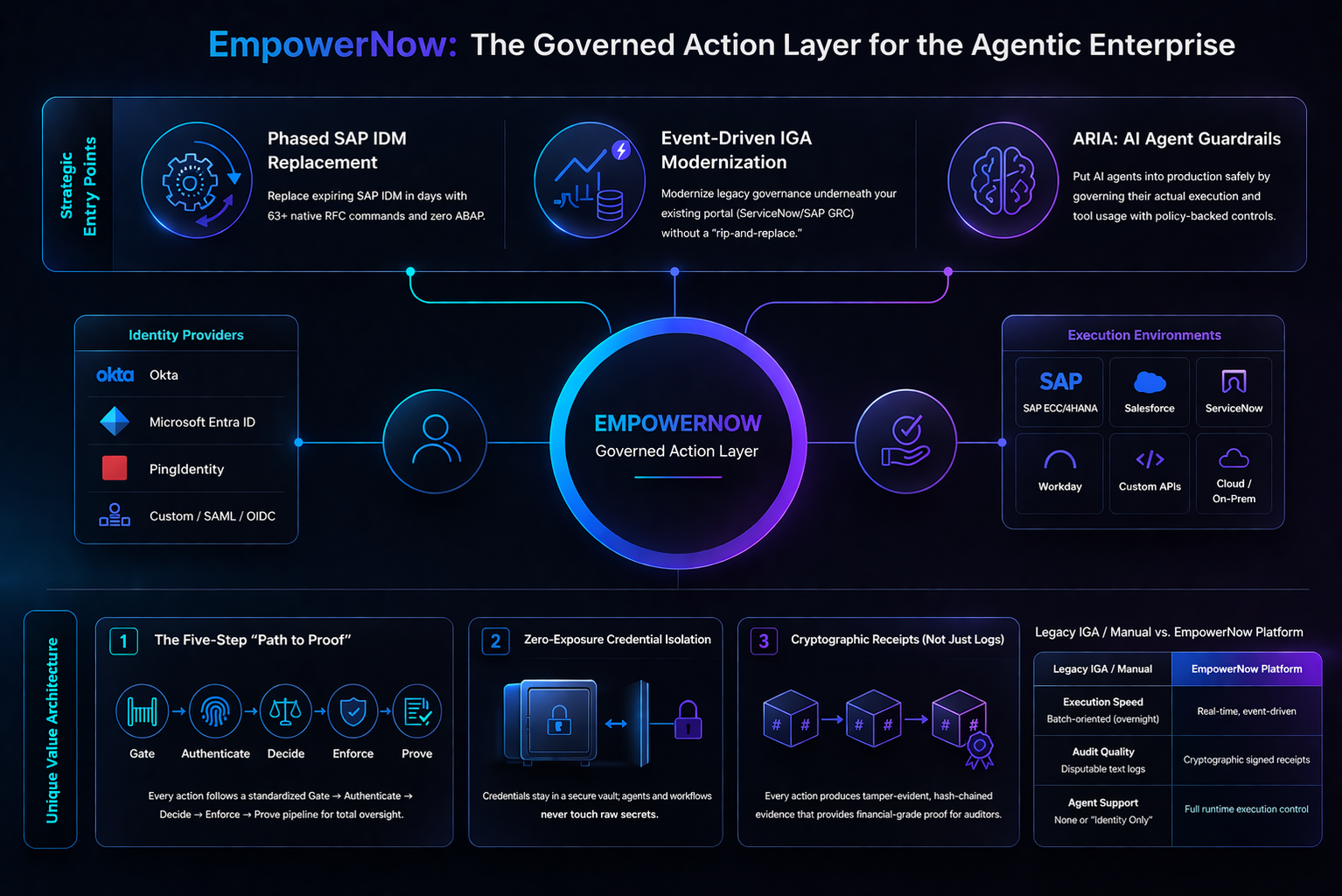
Turn any enterprise action — a user request, an SAP approval, an AI agent call — into a policy-governed operation with runtime authorization, approval, and cryptographic proof. Start with one solution. Expand later without rebuilding the control plane.
Start anywhere. Expand to everything.
Three problems. Three entry points. One control plane underneath. Every entry point gets the same authorization engine, the same proof chain, the same orchestration — scoped to that use on day one.
SAP Identity Migration
SAP IdM is end-of-life. You need governed identity operations for SAP without rebuilding your GRC. The control plane gives you the same authorization engine and proof chain that governs every other EmpowerNow solution — plus six SAP connectors and 63 RFC commands.
Identity Governance
Legacy IGA is brittle and slow. You need governance that handles modern workloads — cloud, SaaS, agents — without ripping out your portal. The control plane gives you policy-driven governance underneath your existing front door.
Agent Runtime Controls
AI agents are shipping without controls. You need runtime execution control — authorization, credential isolation, approval gates, and proof. The control plane governs what agents actually do.
Then expand — without re-platforming.
Started with SAP? Add IGA governance for cloud identities — same policies, same proof chain, same entitlement ledger, no second deployment. Started with ARIA? Add identity governance for the humans behind the agents. Every expansion reuses the control plane you already have.
policy model to learn
re-integration when you expand
proof chain reuse across solutions
How the control plane works
Every governed action — whether triggered by a user, an external system, a workflow, or an AI agent — follows the same five-step path.
A request arrives from
any source
PDP evaluates. Allow,
deny, or escalate
Governed instruction
with constraints
Credentials isolated.
Fail-closed
Cryptographic receipt.
Hash-chained
Same path for a portal user, a REST call, an SAP GRC approval, a governance workflow, or an AI agent.
Technical deep-dive See the control plane in action: two paths, one engine
Path 1 — SAP GRC Approval
A role approval fires in SAP GRC. The event bus normalizes it into a standard event envelope. The PDP evaluates: is this user entitled to this role in this SAP system? The orchestration engine creates a governed directive, retrieves credentials from the vault (tokens never leave the server), and provisions the role via the SAP RFC connector. A cryptographic receipt is written — request, policy decision, execution result, hash-chained to the previous receipt. The entitlement ledger updates with a reference-counted assignment. If the role is later revoked, the ledger proves nothing else breaks.
Path 2 — AI Agent Requests a Jira Update
An AI agent requests a Jira ticket update through the MCP Gateway. The same PDP evaluates: does this agent have a valid delegation from this user for this operation? The orchestration engine creates a governed directive, retrieves the user's Jira OAuth token from the vault (the agent never sees it), and executes the update. A cryptographic receipt is written — same format, same hash chain, same proof structure as the SAP receipt above. The auditor sees the same evidence regardless of whether a human, a workflow, or an agent triggered the action.
What's underneath the control plane
Five shared components make this possible. The Authorization Engine (AuthZEN-compliant PDP) — one policy model for users, APIs, workflows, and agents. The Event Bus (Kafka-backed) — events from any source trigger the same policy-to-proof pipeline with exactly-once semantics. The Entitlement Ledger — reference-counted assignments with safe revocation. The Orchestration Engine — workflow execution, credential isolation, WAITING contracts, connector runtime. The Proof Chain — cryptographic receipts, hash-chained, tamper-evident. These are the same running instances across every solution — not copies, not wrappers. A policy written for SAP applies to agents. A proof receipt from IGA looks identical to one from ARIA.
The data model
Seven primitives underpin the entire platform: Identity, Account, Entitlement, Assignment, Operation, Decision, and Proof. Every solution — SAP, IGA, ARIA, Authorization, Automation — reads and writes these same primitives. That is why expanding from one solution to another is configuration, not integration. Built on open standards: AuthZEN, MCP, OAuth 2.1, OIDC, DPoP, RAR.
What every entry point inherits
Not add-ons. Built into the control plane. Every solution gets these because every solution runs on the same engine.
Runtime Execution Control
Authorize, isolate, approve, and prove every action — whether triggered by an agent, a workflow, or an API call. Patented.
See the ARIA trust stack →Cryptographic Proof Chain
Every action produces a tamper-evident receipt — not a log entry. Receipts are hash-chained per agent, per user, per workflow. Auditors get proof.
See how it works →BYO Front Door
Keep ServiceNow, SAP GRC, or any portal as the user-facing surface. The control plane governs underneath — APIs and events are mandatory, suite UX is optional. Your portal on top, our engine below.
Deployable by your team, not ours.
The platform is architecturally designed for partner and customer self-deployment. APIs and events are mandatory — the suite UX is a replaceable layer. Your SI deploys, your team operates, the control plane scales.
Use the authorization engine, event bus, orchestration, and proof chain behind your own UX. No EmpowerNow UI required.
Keep your portal for user-facing workflows. Use EmpowerNow's admin console for policy authoring, analytics, and agent management.
Use the complete EmpowerNow experience — portal, admin, agent hub, workflow designer, and analytics — all on the same control plane.
The full picture
Three entry points. One governed action layer. Every action authorized, executed, and proved.
Click to view full size
Already using Okta, Entra ID, SailPoint, or One Identity?
EmpowerNow isn't a replacement for your identity provider or IGA portal — it's the governed action layer underneath. Keep your front door. We handle what happens after the decision: execution, credential isolation, and proof.
See how the control plane supports your use case.
We'll walk you through the platform scoped to SAP, IGA, ARIA, or the full stack — and show how expansion works when you're ready.