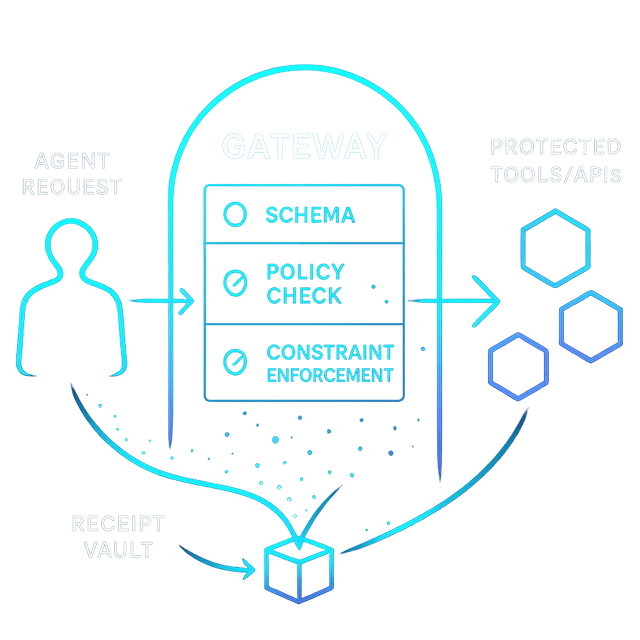
ARIA MCP Gateway
Enforce policy everywhere — pre‑exec governance for agents and tools.
Key advantages
How it works
- Validate ARIA Passport and session.
- Check policy for requested tool and operation.
- Enforce constraints and obligations; call tool.
- Write a signed, hash‑chained receipt.
Guardrails at the edge
Gateway enforces the PDP's guardrails where calls enter: scope and parameter allow‑lists, egress rules, anti‑injection checks, and budget stops. Safe by default, fast in practice.
PDP decides. Gateway enforces.
Every PDP permit can carry constraints (synchronous bounds) and obligations (follow-on duties). The Gateway is the first-party PEP that makes them real:
Constraints (sync, pre-exec)
- Egress allowlists — only approved API hosts
- Parameter allowlists — strip unexpected fields
- Data scope injection — row-level filters
- Token & output caps — truncate at boundary
- Budget stops — 402 before tokens are spent
Obligations (async, around exec)
- Audit log — decision + execution context
- Signed receipt emission — JWS with policy hash
- Notification — alert on high-risk permits
- Kafka decision events — downstream pipelines
Constraints and obligations live inside the AuthZEN context object — the spec's extension point. A generic PEP that only reads decision still works. The Gateway reads the full payload. See the authorization engine →
Plan JWS (per step)
{
"step": 3,
"tool": "billing.export",
"params_fingerprint": "sha256-...",
"schema_hash": "sha256-...",
"iat": 1738020000
}
Gateway verifies the JWS signature and payload fields to ensure the call matches the planned step.
Schema pins & allowlists
{
"schema": { "id": "billing.export", "version": "2.3.1", "hash": "sha256-..." },
"params_allow": ["account_id", "month"],
"egress_allow": ["https://api.example.com"]
}
Pins prevent drift; parameters and egress are enforced at the boundary with PDP constraints.
Budget control: pre‑gate + settle
The PDP checks live budgets before a call (no tokens spent). For streams, Shield reserves a cap and truncates output the instant the budget boundary is reached.
Related reading
Ready to see it live?
Book a 15-minute walkthrough with an engineer. We'll map ARIA MCP Gateway to your architecture, show real event flows, and answer every technical question.