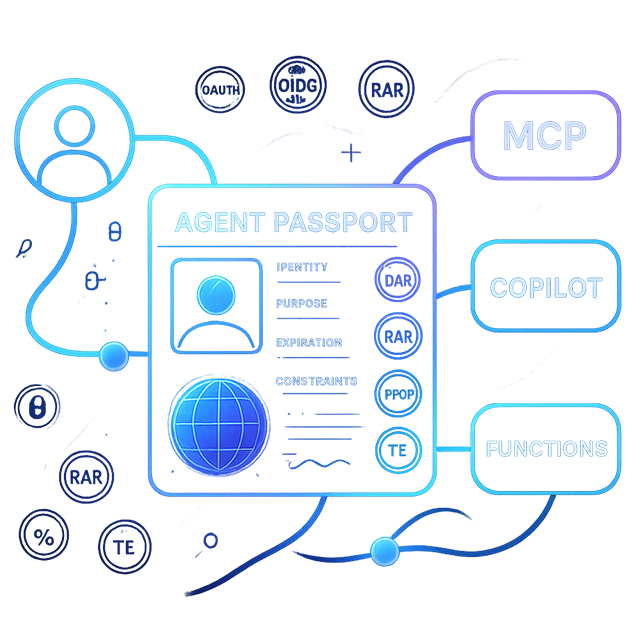
IdP for AI agents
Issue purpose‑bound Agent Passports (TE + RAR + DPoP) with consent, budgets, and schema/plan pins—made for agents, not browsers.
Key advantages
Why purpose‑built for agents
- Agent→user binding; authorize on
sub, recordact.sub, keep client inazp - Batched capability asks (RAR) with optional PAR/JARM
- Consent at issuance; obligations handled before tokens mint
- Proof‑of‑possession (DPoP) for agent runtimes
- Resource‑targeted audiences (RFC 8707) → fewer 401s
Using External IdPs with EmpowerNow
Federate to your corporate IdP (Microsoft Entra ID, Okta, Auth0) for login, then complete OAuth/OIDC locally so you retain control of token issuance, claims, and policy.
Use cases
- Standardize tokens across apps while using the corporate IdP for login
- Migrate or multi‑IdP with a unified claims contract
- Step‑up and consent based on risk/policy—even after upstream auth
- Fine‑grained API authorization with consistent scopes/claims
- Developer tokens and introspection alongside JWTs
Federate but orchestrate
- Redirect to upstream for login; return and orchestrate locally
- Apply obligations (step‑up MFA, consent, risk) and bind sessions
- Outcome parity with “authentication actions” via policy‑driven rules
Collaborative adaptive authentication
- Normalize upstream attributes to canonical claims; decide locally
- Emit identity events for analytics and adaptive posture
Standards we implement for agents
Auth Code + PKCE, Refresh, Client Credentials, Introspection. Optional: PAR, JARM‑style JWT responses, CIBA, DPoP, RFC 8693 Token Exchange, JWE/JWS. Discovery advertises supported grants/algorithms; middleware can enforce FAPI‑style rigor.
- RFC 8693 Token Exchange (OBO)
- RAR (batched capabilities) + PAR/JARM
- DPoP (RFC 9449) token binding
- RFC 8707 Resource Indicators (audience)
- OIDC Discovery + JWKS
Minimal RAR object
{
"authorization_details": [
{
"type": "tool",
"actions": ["invoke"],
"resource": "billing.export",
"locations": ["https://api.example.com"],
"dat": { "purpose": "monthly_report" }
}
]
}
Claims & scopes
- Canonical identity‑first claims with provenance (`orig_iss`, `orig_sub`)
- Composable claims merged from upstream + internal sources
- Per‑client customization without leaking provider specifics
- Introspection parity for local/external tokens
Architecture at a glance
- Login at corporate IdP → return to EmpowerNow
- Orchestrate obligations and assurances
- Issue policy‑controlled tokens / introspection with canonical claims
- Enforce with PDP/services; analytics feed adaptive auth
Getting started
- Configure upstream provider (discovery/JWKS, redirect URIs)
- Enable federation and mapping
- Define canonical claims and any internal sources
- Enable advanced features as required; verify via discovery
- Test end‑to‑end (login, step‑up, issuance, introspection)
GitHub Admin Passport
Scope + step‑up enforced.
Copilot delegated action
Consent before issuance.
Related reading
Ready to see it live?
Book a 15-minute walkthrough with an engineer. We'll map IdP for AI agents to your architecture, show real event flows, and answer every technical question.
Beyond authentication: orchestrated identity journeys
The IdP doesn't just authenticate — it orchestrates. When the PDP says "this user must complete X first," the Interaction Substrate pauses the OIDC authorize flow, runs obligation-driven steps, collects evidence, and resumes with full PKCE integrity.
B2B partner onboarding
Self-service signup, email verification, credential enrollment, org activation — all on the same substrate. Learn more →
Progressive profiling
PDP evaluates profile completeness on every login. Missing attributes trigger inline collection — no separate enrollment portal.
Passkey enrollment
Two strategies: soft nudge (skippable) and policy-driven mandatory. Both use the same substrate with WebAuthn endpoints.
New journeys — step-up MFA, consent refresh, terms acceptance, identity proofing — require a PDP policy and a config change, not code. Deep dive: Identity Orchestration →
Audience control (RFC 8707)
Set the resource and we mint the right audience—no more 401s from mismatched aud.
Identity ARNs & federation
Identity‑first subjects across IdPs (account ARN → identity ARN) mean you write policy once and reuse everywhere.
Consent at issuance
If policy requires consent, issuance pauses with a standards‑friendly authorization_pending and resumes when approved.
- Subject‑only
- Manager‑approved
- Dual approvals
Dev‑tool access (PATs)
Scoped Personal Access Tokens for OpenAI/Anthropic proxies—no vendor keys in clients. Introspect, short cache, enforce scopes, emit receipts.
How the Passport is used
- Passport
- PDP decision
- Gateway guardrails
- Receipt
AI scenarios
Agent on‑behalf‑of
OBO with sub/act/azp and delegation id.
Batched capability ask
RAR across tools; single mint.
DPoP‑bound tool call
Sender‑constrained tokens for agents.
Proof & performance
- Discovery/JWKS for easy verification
- RAR snippet and examples in docs
- P95 issuance targets with cache
FAQ
- Replace corporate IdP? No—federate for login, issue Passports here.
- Delegation for every call? Only agents and elevated service routes.
- 401 audience? Use
resource(RFC 8707) to setaudprecisely.